Full compliance from day one
Personio's airtight system offers a safe place for all of your employee data (with the innovation to match).
Find out moreHR Data Security UK: GDPR Compliance & Employee Data Protection Guide

Employee data is among the most sensitive information your organisation holds: from bank details and health records to right-to-work documents and disciplinary files. A failure to protect it can result in fines of up to £17.5 million or 4% of global turnover, whichever is higher. In 2025, Capita received a £14 million penalty after a ransomware attack exposed the personal data of 6.6 million individuals.
This guide covers the UK GDPR requirements specific to HR, how to handle data subject access requests, how to respond to a data breach, what retention periods apply to employee records, the boundaries of lawful employee monitoring, and what security certifications to look for in HR software.
Contents
- 1What is HR Data Security? (UK Definition)
- 2UK GDPR Requirements for HR Teams (2026)
- 3Employee Data Types & Protection Requirements
- 4How to Handle Data Subject Access Requests (DSARs)
- 5Data Breach Response Plan for HR Teams
- 6Common HR data breach scenarios
- 7UK HR Data Security Case Studies: What Went Wrong
- 8Technical Security Measures for HR Systems
- 9International Data Transfers: Post-Brexit Rules
- 10Employee monitoring and privacy: UK legal boundaries
- 11Data retention schedules for UK HR teams
- 12Security Certifications to Look for in HR Software
- 13Preparing for an ICO Audit: HR Checklist
- 14HR Data Security Best Practices: 2026 Checklist
- 15How Personio keeps your employee data secure and compliant
- 16FAQs: HR Data Security & GDPR UK
What is HR Data Security? (UK Definition)
HR data security refers to the protection of employee personal data against unauthorised access, loss, or misuse, as required by UK GDPR and the Data Protection Act 2018. This includes securing sensitive information such as bank details, health records, right-to-work documents, and performance data. UK employers must implement appropriate technical and organisational measures (Article 32) including encryption, access controls, and staff training.
Term | What it covers |
Compliance | Following all HR laws: employment law, health & safety, payroll, and tax obligations |
Data security | Specifically protecting employee personal data under UK GDPR and the Data Protection Act 2018 |
These two areas overlap, but data security is a distinct discipline with its own legal obligations, enforcement regime, and technical requirements. For full HR compliance guidance beyond data protection, visit our guide.
UK GDPR Requirements for HR Teams (2026)
The UK GDPR sets out specific obligations that apply directly to how you collect, store, and handle employee personal data. These are the five core areas every HR team in the UK must understand.
1. Lawful basis for processing (Article 6)
Every time you process employee data, you must be able to point to one of six lawful bases. In an HR context, the four you will rely on most are:
Employment contract: payroll, administering benefits, managing the employment relationship.
Legal obligation: right-to-work checks, pension auto-enrolment, PAYE and tax records.
Legitimate interests: recruitment screening, performance management (requires a documented Legitimate Interest Assessment).
Consent: optional benefits, employee photos in directories; only valid where employees have a genuine free choice.
Document the lawful basis for every processing activity in your Article 30 records of processing. If you cannot articulate a basis, you should not be processing the data.
2. Data subject rights (Articles 13–22)
Employees hold a bundle of rights over the personal data you hold on them. Your HR processes must be able to action each of these within the required timeframes:
Right to be informed (Articles 13-14): provide a privacy notice at the point of hire covering what data you collect, why, how long you keep it, and who sees it.
Right of access (Article 15): respond to data subject access requests (DSARs) within one calendar month; see the DSAR section below for the full process.
Right to rectification (Article 16): correct inaccurate employee records promptly, for example an incorrect job title, salary figure, or address.
Right to erasure (Article 17): former employees may request deletion of their data; you can decline where retention is required by law or to defend a legal claim.
Right to data portability (Article 20): rarely applicable in HR; relevant only where processing is based on consent or contract and carried out by automated means.
Failure to respond to a DSAR within the one-month deadline is one of the most common grounds for an ICO complaint. Build a documented, tested process before you receive a request.
3. Security measures (Article 32)
Article 32 requires you to implement technical and organisational measures appropriate to the risk your processing presents. For HR data, this typically means:
Pseudonymisation and encryption: protect data at rest (AES 256) and in transit (TLS).
Ability to restore availability: automated backups with tested point-in-time recovery, protecting against ransomware and system failure.
Regular testing of security measures: annual penetration testing, quarterly vulnerability scans, and ongoing monitoring.
Staff training: all employees who handle personal data must understand their obligations; training should be refreshed annually and completion recorded.
The ICO, working with the National Cyber Security Centre (NCSC), has published a set of security outcomes providing practical guidance on what 'appropriate' looks like for different types of organisation. See the Technical security measures section below for a full breakdown.
4. Breach notification (Articles 33-34)
When a personal data breach occurs, you have specific notification obligations:
72-hour ICO notification: if the breach is likely to result in a risk to individuals' rights and freedoms, report to the ICO within 72 hours of becoming aware of it; you can report in phases if the full picture is not yet clear.
Employee notification: if the breach is likely to result in high risk to individuals (for example, exposure of payroll or health data), notify affected employees directly and without undue delay.
Documentation requirements: you must log all breaches under Article 33(5), whether notifiable or not, recording the facts, effects, and remedial action taken.
The 72-hour window starts from when your organisation becomes aware of the breach — not when the incident occurred. See the Data breach response section for the full five-step process.
5. Data protection by design (Article 25)
Data protection must be built into new HR processes from the outset, not retrofitted. In practice this means:
Privacy from the start of new HR systems: conduct a Data Protection Impact Assessment (DPIA) before deploying new HR technology; consider access controls, data minimisation, and encryption at the design stage.
Data minimisation in recruitment forms: only collect information you genuinely need; do not request date of birth, nationality, or protected characteristics unless there is a clear, documented reason.
Article 25 also requires privacy-by-default: your systems should process the minimum personal data necessary unless the individual actively chooses otherwise.
2026 update: the Data (Use and Access) Act 2025
The Data (Use and Access) Act 2025 (DUAA) received Royal Assent on 19 June 2025. Most of its key data protection provisions came into force on 5 February 2026, with further changes – including a new mandatory complaints right – scheduled for 19 June 2026. The DUAA amends, but does not replace, the UK GDPR and the Data Protection Act 2018.
The changes most relevant to HR teams are:
DSARs: the DUAA codifies that only 'reasonable and proportionate' searches are required; this is particularly helpful for large organisations with complex IT infrastructure, but the one-month response deadline remains unchanged.
Automated decision-making: restrictions have been relaxed; employers in the UK can now more easily use AI and algorithmic tools in recruitment, performance management, and workforce planning, provided appropriate safeguards are in place; this diverges from the EU GDPR position.
Recognised legitimate interests: a set of pre-approved legitimate interest bases has been introduced for specific purposes, such as sharing employee data with law enforcement in a workplace security incident, removing the need for a balancing test in those cases.
Mandatory complaints procedure: from 19 June 2026, employers must provide a formal route for employees to raise data protection complaints directly; complaints must be acknowledged within 30 days and investigated without undue delay.
International transfers: the standard for transfers to third countries has been adjusted to 'not materially lower' than UK protections, replacing the previous 'essentially equivalent' test; updated ICO guidance on transfers was published in early 2026.
The UK is now diverging from EU GDPR in several areas. Organisations that also operate in the EU should review which regime applies to each processing activity and ensure their policies reflect both where necessary.
Employee Data Types & Protection Requirements
Not all employee data carries the same level of risk. Understanding how to classify what you hold is the first step towards proportionate protection.
Data type | Examples | Classification | Key protection requirement |
Standard personal data | Name, address, job title, salary | Standard | Encryption in transit; role-based access |
Special category data | Health records, trade union membership, ethnicity data | Enhanced | Explicit condition under Article 9 required |
Criminal conviction data | DBS check results | Restricted | Specific legal basis required; limited retention |
Right-to-work documents | Passport copies, visa documents | Standard | Retain 2 years post-employment; secure storage |
Payroll and financial data | Bank details, tax codes, pension contributions | Standard/Sensitive | Encryption; retain 6 years (HMRC requirement) |
Performance and disciplinary records | Appraisals, written warnings | Standard | Restrict access; retain 6 years post-employment |
How to Handle Data Subject Access Requests (DSARs)
Under Article 15 of the UK GDPR, any employee (current or former) can request a copy of all the personal data you hold about them. This is called a data subject access request (DSAR) or subject access request (SAR). The terms are used interchangeably; the ICO typically uses SAR.
You must respond without undue delay and within one calendar month of receiving the request. That is a calendar month, not 30 days. You can extend the deadline by up to two further months if the request is complex or you have received multiple requests from the same individual, but you must notify the requester within the original month and explain why.
There is no formal wording required: a verbal request, a social media message, or an email asking 'what data do you have on me?' can all constitute a valid DSAR. The clock starts from the day of receipt, even if that day falls on a weekend or bank holiday.
Step 1: Receive and log the request
Record the date received, the requester's details, and the scope of the request. Acknowledge receipt promptly, ideally within a few days. The one-month clock has already started.
Step 2: Verify identity
Before releasing data, confirm the requester is who they say they are. Proportionate verification might mean asking for an employee ID number and date of birth, or requesting photo ID for a high-sensitivity request. Do not use verification checks to delay or discourage legitimate requests, the ICO takes a dim view of this.
Step 3: Search all data sources
A DSAR response must be comprehensive. Search your HR system, payroll records, performance management files, emails mentioning the employee, disciplinary notes, manager comments, and any other system where personal data may be held.
Step 4: Compile the response
Provide a copy of the personal data held, together with supplementary information: the purposes of processing, the categories of data, who has access to it, how long you keep it, and the employee's right to complain to the ICO. If data also belongs to a third party, redact it carefully before disclosure.
Step 5: Deliver within one calendar month
The response must be free of charge in almost all circumstances, and provided in a commonly used electronic format if the request was made electronically. Missing the deadline exposes you to an ICO complaint and potential enforcement action.
Common pitfalls to avoid
Missing emails or manager notes stored outside the main HR system
Over-redacting data belonging to the requester, or under-redacting data belonging to third parties
Charging for standard requests, this is not permitted
Failing to provide the supplementary information required alongside the data copy
Data Breach Response Plan for HR Teams
A personal data breach is any security incident that affects the confidentiality, integrity, or availability of personal data. The ICO defines this broadly: it includes accidental disclosure, ransomware attacks, lost laptops, and emails sent to the wrong recipient. Not every breach requires ICO notification, only those likely to pose a risk to individuals' rights and freedoms.
Step 1: Containment (immediate)
Isolate the affected system or account. Disable compromised credentials. Stop the unauthorised access and preserve evidence for your investigation. Speed matters: the 72-hour notification window starts from when you become aware of the breach.
Step 2: Assessment (within 24 hours)
Determine what data was affected, how many employees are involved, and the likely risk to individuals. Ask: could this data be used to harm the people it relates to – financially, reputationally, or otherwise? Document your assessment.
Step 3: Notification to the ICO (within 72 hours)
If the breach is likely to result in a risk to the rights and freedoms of individuals, you must notify the ICO without undue delay and, where feasible, within 72 hours of becoming aware of it. The ICO recognises you may not have the full picture within 72 hours: Article 33(4) of the UK GDPR allows you to submit information in phases. Report early and update later.
Your notification to the ICO must include: the nature of the breach, the approximate number of individuals affected, the likely consequences, the measures you are taking to address it, and your data protection officer's contact details (if you have one). Use the ICO's online breach report portal.
Step 4: Notification to affected employees (if high risk)
Where the breach is likely to result in high risk to individuals, for example, the exposure of bank details or health records, you must also notify those employees directly, without undue delay. Tell them what happened, what data was affected, what the likely consequences are, and what steps they can take to protect themselves.
Step 5: Post-incident review
Document the lessons learned. Update your security measures. Retrain staff where human error contributed to the breach. Test your recovery procedures. Article 33(5) requires you to maintain records of all personal data breaches, whether or not they were notifiable.
Common HR data breach scenarios
The five scenarios below account for the majority of personal data breaches reported by HR teams. Each one is preventable with the right controls in place.
Scenario | Data at risk | Likely notifiable to ICO? | Prevention |
Payroll file emailed to the wrong recipient | Bank details, salaries, tax codes | Yes: financial data, high harm potential | Mandatory recipient check before send; encrypted attachments; Data Loss Prevention (DLP) rules on email |
Laptop or USB stick lost or stolen – unencrypted | Any employee records stored locally | Yes: if data is unencrypted and accessible | Full-disk encryption (BitLocker/FileVault) as policy; remote wipe capability; no unencrypted USBs |
Phishing attack compromising HR credentials | All data accessible via the compromised account | Yes: likely wide exposure | MFA on all HR system accounts; phishing simulation training; anomalous login alerts |
Misconfigured cloud storage – employee files publicly accessible | Any files in the affected bucket or folder | Yes: unauthorised public disclosure | Automated misconfiguration scanning; default-deny permissions on cloud storage; quarterly access reviews |
Former employee retaining system access after leaving | Depends on role: potentially payroll, disciplinary, all-employee data | Depends on whether access was used; likely yes if accessed | Automated leavers workflow: accounts disabled on last day; access reviewed at offboarding |
ICO breach notification checklist
Use this checklist as your internal verification step before submitting a notification to the ICO. The ICO's online breach report form must be completed in a single session and cannot be saved mid-way through, have these details ready before you start.
Section | What to prepare |
Nature of the breach | Was it a confidentiality breach (unauthorised disclosure), integrity breach (unauthorised alteration), or availability breach (loss/destruction)? Describe how it occurred. |
Categories of personal data affected | Which data types were involved: names, bank details, health data, right-to-work documents, disciplinary records? Note whether special category data is affected. |
Approximate number of individuals affected | How many employees, former employees, or job candidates are involved? An estimate is acceptable at initial notification. |
Approximate number of records affected | How many individual data records were compromised: not the same as individuals if each person has multiple records. |
Name and contact details of DPO or data protection contact | If you have a DPO, provide their name and contact details. If not, provide the most senior person responsible for data protection. |
Likely consequences of the breach | What harm could result for individuals: financial loss, identity theft, reputational damage, discrimination, physical harm? Assess severity and likelihood. |
Measures taken or proposed to address the breach | What containment steps have been taken? What remedial action is planned or under way? What will be done to prevent recurrence? |
Whether affected individuals have been notified | If the breach poses high risk to individuals, have they been informed directly? If not, when and how will this happen? |
If you cannot provide all the required information within 72 hours, submit what you have and explain the reason for the delay. Article 33(4) of the UK GDPR explicitly permits phased reporting: notify early and update the ICO as your investigation progresses. Report online at ico.org.uk, or call the ICO's breach helpline on 0303 123 1113 during office hours.
Breach notification template: notifying affected employees
Where a breach is likely to result in high risk to individuals, for example, exposure of payroll data, health records, or right-to-work documents, you must notify affected employees directly and without undue delay (Article 34, UK GDPR). The notification must explain what happened, what data was involved, what harm may result, and what steps employees can take to protect themselves.
The following structure covers all required elements under Article 34(2):
Section | Required content | Example wording |
Opening, nature of the breach | Plain-language description of what happened and when you became aware of it | "We are writing to inform you of a personal data incident that came to our attention on [date]. On [date of incident], [brief description – e.g., a payroll file containing employee salary data was sent to an incorrect email address]." |
Data affected | Specific categories of data involved, so individuals can assess their personal risk | "The data involved includes: your name, job title, salary and bank account details [amend as applicable]. No health, disciplinary, or right-to-work information was included in this incident." |
Likely consequences | Honest, proportionate assessment of the harm that could result | "There is a risk that this information could be used for financial fraud or identity theft. We believe the risk is [low/medium/high] because [explain why – e.g., the recipient has confirmed deletion]." |
Measures taken | Steps the organisation has taken or is taking to address the breach and reduce harm | "We have [contacted the unintended recipient and requested secure deletion / disabled the compromised account / reported the incident to the ICO]. We are also [describe any further remedial steps]." |
Steps employees can take | Practical protective action, what individuals can do to protect themselves | "We recommend you: monitor your bank statements for any unusual activity; contact your bank immediately if you see transactions you do not recognise; consider placing a CIFAS protective registration if you are concerned about identity fraud." |
Further contact | Who to contact with questions, and confirmation of ICO complaint right | "If you have questions or concerns, please contact [name/role] at [email/phone]. You also have the right to lodge a complaint with the Information Commissioner's Office at ico.org.uk or by calling 0303 123 1113." |
Keep a copy of every notification sent, the date sent, and confirmation of delivery. This forms part of your Article 33(5) breach documentation and may be requested by the ICO during an investigation or audit.
UK HR Data Security Case Studies: What Went Wrong
The four cases below are drawn directly from ICO enforcement decisions. Each involved failures your HR team can act on today. All penalty amounts are confirmed from published ICO enforcement notices. You can browse the full register of ICO enforcement actions here.
Case 1: Capita – £14 million (October 2025)
On 22 March 2023, a Capita employee downloaded a malicious file. A high-priority security alert was raised within ten minutes, but the affected device was not quarantined for 58 hours, far exceeding Capita's own one-hour target response time. During that window, the attacker gained administrator privileges, moved laterally through the network, exfiltrated nearly one terabyte of data, and later deployed ransomware.
The breach affected 6.6 million individuals across 325 pension schemes, exposing pension records, employment records, financial data, and special category data including health information and criminal records. The ICO fined Capita plc £8 million and its subsidiary Capita Pension Solutions £6 million —a combined £14 million — in October 2025.
HR lesson: MFA is mandatory for all HR system access, particularly administrator accounts. A breach alert is only as useful as the response it triggers – your incident response plan must have tested escalation procedures with defined timelines.
Articles breached: 5(1)(f) – integrity and confidentiality principle; 32 – security of processing.
Case 2: British Airways – £20 million (October 2020)
In June 2018, an attacker gained access to the British Airways network using compromised credentials stolen from a Swissport employee, a third-party contractor whose account had no MFA enabled. The attacker moved through the network undetected for over two months, ultimately injecting malicious code that harvested payment card data and personal information from the BA website.
The breach was not discovered by BA itself: the company was alerted by a third party on 5 September 2018. The personal data of approximately 430,000 customers and staff was potentially compromised, including names, addresses, payment card numbers, CVV codes, and employee login credentials.
The ICO issued a Notice of Intent to fine BA £183 million in 2019. Following BA's representations, a reconsideration of the facts, and a £4 million COVID-19 reduction, the final penalty was set at £20 million in October 2020 – at the time the largest fine ever issued by the ICO.
HR lesson: Third-party accounts with access to your systems require the same MFA controls as internal staff. Breach detection protocols must be active, not passive, BA did not detect this breach itself after two months of active exfiltration.
Articles breached: 5(1)(f) – integrity and confidentiality principle; 32, security of processing.
Case 3: Ticketmaster UK – £1.25 million (November 2020)
In February 2018, malicious code was injected into a third-party chatbot that Ticketmaster had placed on its payment pages. The chatbot was provided by a supplier called Inbenta. The code silently harvested payment card details and personal information entered by customers.
Ticketmaster was alerted to potential fraud by Monzo Bank as early as April 2018 but took nine weeks to begin monitoring traffic through its payment page. The breach potentially affected 9.4 million individuals in the EEA, including 1.5 million in the UK. Some 60,000 Barclays Bank payment cards were confirmed compromised.
The ICO issued a £1.25 million Monetary Penalty Notice on 13 November 2020, over two years after the breach began and more than two and a half years after GDPR came into force. Ticketmaster appealed the penalty notice to the First-tier Tribunal. The appeal was stayed pending parallel High Court proceedings.
HR lesson: Every third-party tool with access to employee or candidate data, applicant tracking systems, background-check providers, payroll integrations, must be subject to documented vendor due diligence, proportionate to the sensitivity of the data involved. Contractual assurances are not a substitute for technical controls.
Articles breached: 5(1)(f), integrity and confidentiality principle; 32, security of processing.
Case 4: Interserve Group – £4.4 million (October 2022)
In March 2020, a phishing email landed in an Interserve accounts team mailbox. Interserve's system neither quarantined nor blocked it. An employee forwarded it to a colleague, who opened the attachment and triggered a malware installation. The anti-virus software quarantined the malware and sent an alert — which Interserve failed to properly investigate. Had it done so, it would have found the attacker still had access to company systems.
The attacker went on to compromise 283 systems and 16 accounts, uninstalled Interserve's anti-virus solution, and encrypted the personal data of up to 113,000 current and former employees. The compromised data included bank account details, national insurance numbers, contact details, and special category data covering ethnic origin, religion, disability, sexual orientation, and health information held across four HR databases.
The ICO's investigation found that Interserve had been failing to maintain adequate security measures since March 2019 (well before the attack) and issued a £4.4 million Monetary Penalty Notice on 24 October 2022, over two years after the breach occurred. This timeline is typical: ICO enforcement investigations of this scale routinely take one to two years from breach to fine.
HR lesson: An unacted security alert is as dangerous as having no alert at all. Phishing simulation training, up-to-date endpoint protection, and a clear protocol for investigating anti-virus alerts are all required under Article 32.
Articles breached: 5(1)(f), integrity and confidentiality principle; 32, security of processing.
Common patterns across ICO enforcement cases
The patterns that emerge from enforcement actions, where the ICO has found breaches warranting fines, include:
Failure to act on security alerts: Interserve and Capita both had detection systems that worked; the failure was in the response.
No MFA on accounts with access to personal data: present in both the BA and Capita cases.
Inadequate vendor due diligence: the direct cause of the Ticketmaster fine; a growing risk as HR tech stacks become more complex.
Outdated software and unpatched systems: cited by the ICO as a contributing factor in both Interserve and multiple other enforcement cases.
Delayed breach detection and notification: each case above involved a period where the attacker had undetected access that a monitoring control could have shortened.
Technical Security Measures for HR Systems
Article 32 of the UK GDPR does not prescribe specific technologies, it requires measures appropriate to the risk. For HR processing, which typically involves large volumes of sensitive personal data, the following controls are widely recognised as appropriate.
Security control | What it does | Relevance to HR |
AES 256-bit encryption (data at rest) | Protects stored data from unauthorised access | Employee files, payroll records, health data |
TLS 1.3 encryption (data in transit) | Secures data as it moves between systems | Self-service portals, integrations with payroll providers |
Role-based access control (RBAC) | Limits data access to those with a legitimate need | Payroll manager sees salaries; line manager does not |
Multi-factor authentication (MFA) | Prevents unauthorised login if credentials are stolen | All HR system users; mandatory for admins |
Audit trails | Logs who accessed or changed data and when | Essential for breach investigation and ICO audits |
Automated backups | Protects against ransomware and system failure | Daily incremental; tested quarterly for recovery |
Secure data disposal | Ensures deleted data cannot be reconstructed | Required when retention periods expire |
A note on encryption standards
The ICO's guidance, developed in collaboration with the NCSC, does not mandate specific encryption algorithms, the standard is 'appropriate to the risk'. In practice, AES 256-bit encryption for data at rest and TLS 1.3 for data in transit are widely considered current best practice for HR data. When evaluating HR software vendors, ask explicitly for their encryption specification.
Joiners, movers, and leavers
One of the most common access-control failures in HR is the failure to revoke system access promptly when employees leave or change roles. A former employee retaining access to payroll data or employee files is a data breach waiting to happen. Your HR system should support automatic access revocation as part of the offboarding process.
International Data Transfers: Post-Brexit Rules
If your organisation sends employee data outside the UK – whether to an overseas office, an outsourced payroll provider, or a US-based HR software platform – you need to ensure the transfer is lawful.
UK to EU/EEA
The UK currently has an adequacy decision in place with the EU/EEA, meaning data can flow freely between the UK and EU member states without additional safeguards. This position was in place as of March 2026, but organisations should monitor for any divergence as UK data protection law develops independently of EU GDPR.
UK to United States
There is no adequacy decision between the UK and the US. If you transfer employee data to a US-based HR software vendor, payroll provider, or parent company, you will need to rely on International Data Transfer Agreements (IDTAs) or Standard Contractual Clauses (SCCs) with a UK addendum, and carry out a Transfer Impact Assessment (TIA) to confirm that the data is adequately protected in the destination country.
UK to other countries
The ICO maintains a list of countries with adequacy decisions. For transfers to countries without adequacy, you will need appropriate safeguards such as IDTAs. Check the ICO's international transfers guidance at ico.org.uk for the current list.
Employee monitoring and privacy: UK legal boundaries
Many HR teams are unsure how far they can go when monitoring employee activity, particularly with hybrid and remote working now commonplace. The ICO published comprehensive guidance on monitoring workers in October 2023. The short answer is: monitoring is permitted, but it must be lawful, transparent, and proportionate.
You must identify a lawful basis under Article 6 for any monitoring activity. You must also tell employees what monitoring takes place, why, and what data is collected. Covert monitoring — where employees have no knowledge of the surveillance, is only justifiable in exceptional circumstances, such as a suspected criminal investigation, and must be authorised by senior management.
What the ICO guidance says about specific monitoring types
Monitoring type | Generally permitted if... | Key requirement |
Email and internet monitoring | Disclosed in policy with legitimate business purpose | Proportionate; personal emails should not be read |
CCTV in the workplace | For security or health and safety purposes | Clear signage; limited retention (typically 30 days) |
Call recording | For quality, training, or regulatory compliance | Both parties informed at start of call |
Keystroke logging / screen recording | Only where strong justification exists | ICO considers this high privacy risk; requires DPIA |
GPS tracking (company vehicles) | For fleet management or safety purposes | Must not track outside work hours without clear justification |
Biometric data | With explicit consent or legal basis | Special category data; requires DPIA and Article 9 condition |
The ICO also recommends completing a Data Protection Impact Assessment (DPIA) before implementing any monitoring system, even where one is not strictly required by law. For employees working from home, the ICO notes that their reasonable expectation of privacy is higher than in an office setting.
Data retention schedules for UK HR teams
UK GDPR requires you to keep personal data only for as long as necessary. But 'necessary' is defined by a combination of legal obligations, regulatory requirements, and legitimate business needs, and the timelines differ by record type. Below are the key retention periods for UK HR records.
Record type | Minimum retention period | Legal or regulatory basis |
Payroll records (P45, P60, payslips, wage records) | 6 years from end of tax year | HMRC; Limitation Act 1980 |
Right-to-work documents | 2 years post-employment | Immigration, Asylum and Nationality Act 2006 |
Pension and auto-enrolment records | 6 years post-scheme exit | Pensions Act 2004 |
Recruitment records (unsuccessful candidates) | 6–12 months post-recruitment | Discrimination claim limitation period |
Disciplinary and grievance records | 6 years post-employment or case resolution | Employment Tribunal / civil claim limitation period |
Accident and injury reports | 3 years from date of incident | Health and Safety regulations |
Sickness absence records | 3 years post-employment (general); 40+ years if related to occupational exposure | COSHH Regulations (for hazardous substances) |
Performance reviews | Duration of employment + 6 years | Redundancy / dismissal defence |
Training records | Duration of employment + 6 years | Health and safety compliance evidence |
The 6-year benchmark for most HR records aligns with the limitation period for breach-of-contract claims under the Limitation Act 1980. Once a retention period expires, data should be securely deleted or anonymised. Using an HR system to automate deletion rules significantly reduces the risk of retaining data longer than necessary, and the ICO complaint that can follow.
Security Certifications to Look for in HR Software
When evaluating HR software vendors, certifications offer third-party assurance that the vendor's security controls have been independently tested. Here are the key ones to look for.
ISO 27001 (Information Security Management)
The international standard for information security management systems. ISO 27001 certification means the vendor has a systematic approach to managing security risks, including policies, controls, and ongoing audits. Ask to see a current certificate and check which certification body issued it.
SOC 2 Type II (Service Organization Control)
A US-originated but internationally recognised standard that audits a vendor's security, availability, and confidentiality controls over a period of at least six months (Type II). Type II is more rigorous than Type I, which only tests controls at a single point in time. A SOC 2 Type II report gives you evidence that the vendor's security practices are consistently applied.
Cyber Essentials / Cyber Essentials Plus (UK)
A UK government-backed certification scheme that validates basic security hygiene: firewalls, secure configuration, access controls, malware protection, and patch management. Cyber Essentials Plus includes an independent technical verification. This certification is mandatory for UK government contracts and is increasingly expected in public sector supply chains.
ISO 27701 (Privacy Information Management)
An extension to ISO 27001 that adds privacy-specific controls aligned with GDPR and other privacy regulations. ISO 27701 certification indicates the vendor has embedded privacy-by-design processes into their security management system, relevant given HR software's role as a data processor.
Red flags when evaluating vendors
'We're GDPR compliant' stated without supporting documentation
No security certifications of any kind
Refusal to provide a Data Processing Agreement (DPA)
Vague or evasive answers about data storage locations
No incident response procedure or bug bounty programme
Preparing for an ICO Audit: HR Checklist
ICO audits can be triggered by a breach report, an employee complaint, a sector-wide investigation, or random selection. They are not reserved for large organisations, the ICO audits companies of all sizes. Knowing what to expect makes preparation manageable.
What the ICO will typically request
Records of processing activities (Article 30 register): documenting what employee data you process, why, who has access, how long you keep it, and any international transfers.
Employee and recruitment privacy notices: current versions, evidence of updates when processing changed.
Data Protection Impact Assessments: particularly for high-risk processing such as employee monitoring, AI-based recruitment tools, or large-scale profiling.
Data Processing Agreements with vendors: your payroll provider, HR software supplier, and background check services.
DSAR response records: how you handled past requests, response timelines, and the information provided.
Breach notification records: incidents logged, ICO notifications made, evidence of 72-hour reporting.
Security measures documentation: encryption policies, access control matrices, staff training records, penetration test results.
Data retention policy: schedules by record type and evidence of secure disposal.
Preparation checklist
Maintain your Article 30 processing register and review it quarterly
Review employee and recruitment privacy notices annually
Conduct DPIAs for new HR technology and high-risk processing activities
Audit third-party DPAs annually, ensure they reflect current processing
Document your DSAR process and track response times
Test your breach notification procedure at least annually
Commission an annual external security review or penetration test
Run GDPR training for all staff who handle employee data, record completion rates
Review your data retention schedules and delete expired records on schedule
Appoint a Data Protection Officer if your organisation requires one
HR Data Security Best Practices: 2026 Checklist
Use this checklist to audit your organisation's current position against the UK GDPR requirements and NCSC security recommendations covered in this guide. The checklist is organised by category, work through each in turn and note any gaps. A gap is not automatically a breach, but an undocumented gap is a material risk if the ICO investigates.
For an interactive version of this checklist where you can track your progress and calculate a compliance score, see the companion tool at the end of this section.
Technical measures
AES 256-bit encryption for all employee data at rest (employee files, payroll records, health data)
TLS 1.3 encryption for all data in transit (self-service portals, payroll integrations, API connections)
Multi-factor authentication (MFA) enforced for all HR system users — mandatory for administrator accounts
Role-based access controls (RBAC) configured so staff access only the data their role requires
Automated daily backups in place, backup recovery tested at least quarterly
Audit trails enabled and retained for a minimum of 12 months, logs include who accessed or changed data and when
Firewall and intrusion detection/prevention systems active and monitored
Patch management policy in place, critical patches applied promptly (NCSC recommends within 14 days for critical vulnerabilities; 30 days is a common organisational policy)
Antivirus and anti-malware with real-time protection deployed across all systems handling HR data
Secure data disposal process documented, crypto-shredding or equivalent for electronic records; cross-cut shredding for paper
Organisational measures
Data Protection Officer appointed, if required under Article 37 UK GDPR
Article 30 records of processing activities maintained and reviewed at least annually
Employee and recruitment privacy notices provided at point of hire and updated when processing changes materially
Annual GDPR training completed by all staff who handle employee data, attendance records kept
Data retention policy documented, with retention periods set by record type and automated deletion where possible
DSAR process documented with a target response time within one calendar month (the legal deadline under Article 15)
Breach response plan documented and tested at least annually, includes ICO 72-hour notification step
Third-party vendor due diligence completed, signed Data Processing Agreements in place with all processors handling employee data
Data Protection Impact Assessments completed for all high-risk processing activities (employee monitoring, AI-based recruitment tools, biometric data)
Regular security audits conducted, internal quarterly review; independent external audit or penetration test at least annually
Access management
Joiners, movers, and leavers process documented, access provisioned and revoked promptly on role change or departure
Privileged access reviewed quarterly, administrator-level accounts kept to the minimum necessary
Password policy enforced: minimum length (NCSC recommends longer passphrases over short complex passwords); account lockout after failed attempts; passwords changed only when compromise is suspected
Single sign-on (SSO) implemented where possible to reduce credential sprawl
Remote access to HR systems via VPN or equivalent secure connection only
Physical security
Locked storage for paper HR records (personnel files, right-to-work documents, medical certificates)
Clear desk policy in place for any area where HR records are handled
Visitor management process in place, sign-in, escorting, and log retention
Secure disposal bins available for paper containing personal data, cross-cut shredding or confidential waste contractor
Monitoring and response
Security incident log maintained, all incidents recorded regardless of whether ICO notification is required
Threat intelligence monitoring in place, alerts configured for unusual access patterns or data exfiltration attempts
Annual penetration test commissioned from an independent security provider
Monthly vulnerability scanning across systems that process HR data
Security metrics reviewed regularly, access attempts, failed logins, privilege escalations, and DSAR response times
Compliance documentation
Data Processing Agreements in place and reviewed annually with all third-party processors
Consent records maintained where consent is the lawful basis for processing (e.g. optional employee directory photos)
Lawful basis documented for every processing activity in the Article 30 register
International transfer safeguards in place for any employee data sent outside the UK, IDTAs or SCCs with a UK addendum plus Transfer Impact Assessments
Employee monitoring disclosures documented in policy and communicated to all affected employees before monitoring begins
See how Personio helped Polaroid stay GDPR-compliant while reducing administrative burdens on HR staff.
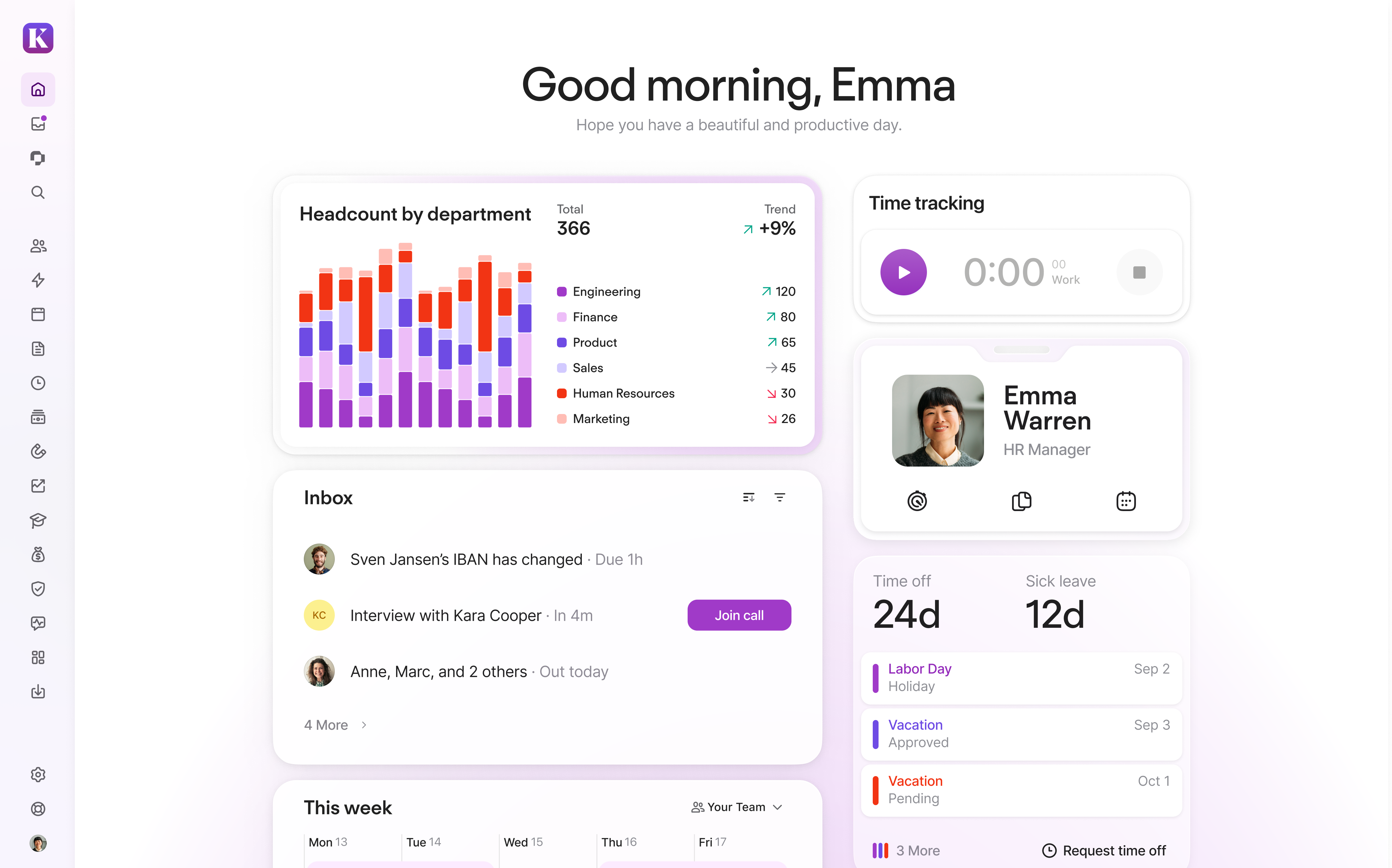
How Personio keeps your employee data secure and compliant
Personio is the Intelligent HR Platform. Our Smart Automations eliminate the busy work so you can focus on the meaningful. Our Dynamic Adaptability allows Personio to meet the needs of your business for today and tomorrow. Our Proactive Insights help every HR team make confident people decisions.
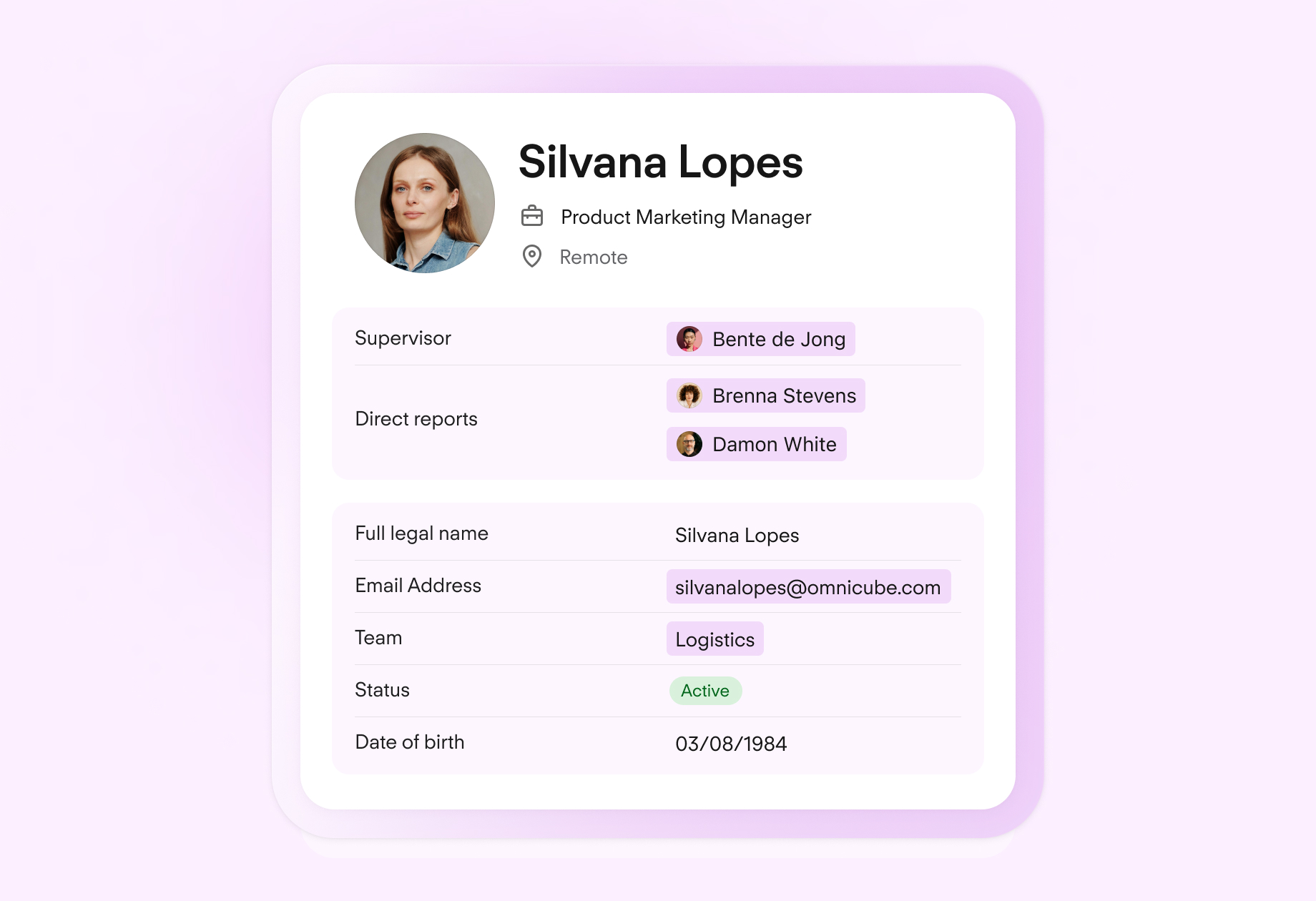
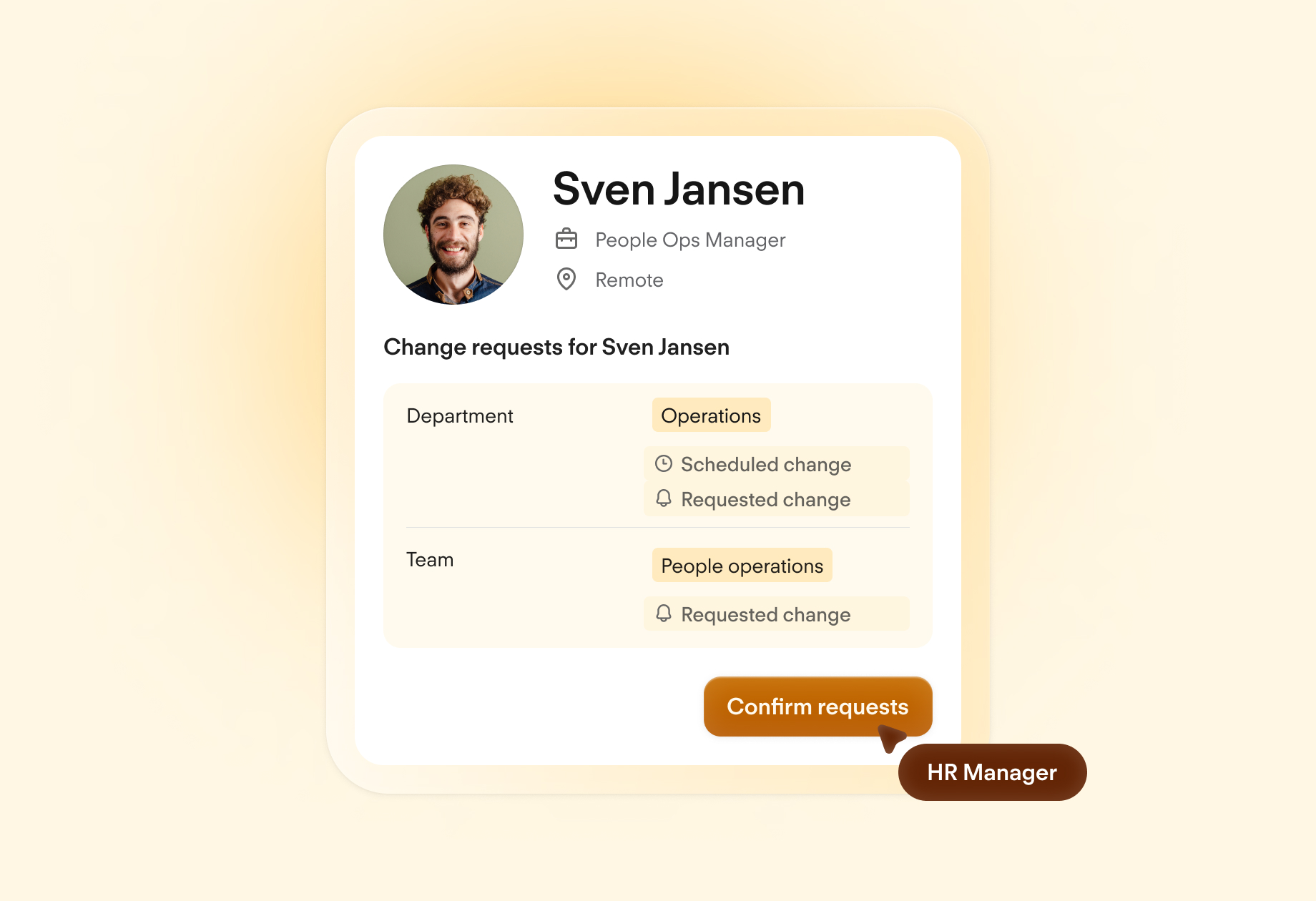
From a data security perspective, Personio is built to help HR teams meet UK GDPR obligations without adding manual overhead. Centralised, encrypted employee files replace email chains and spreadsheets. Automated data retention rules adjust based on employee location, for example, the retention period for absence records in the UK differs from the requirement in Germany, and Personio can manage both. Employee self-service portals allow staff to access and update their own data, supporting transparency and reducing the risk of inaccurate records.
For DSAR responses, Personio's tooling helps HR teams compile an employee's complete data profile from a single system rather than manually searching across disconnected platforms. Role-based access controls mean that only the right people can view payroll data, health information, or disciplinary records, and every access is logged in an immutable audit trail.
Certifications and technical safeguards:
ISO 27001 certified, validated by independent third-party audit on an annual basis
AES 256-bit encryption for data at rest; TLS encryption for data in transit
Multi-factor authentication for all users
Role-based access control with principle of least privilege
GDPR DSAR automation, compile a complete employee data profile from a single centralised record
UK and EU data residency options
Automated data retention rules by employee location and data type
Discover secure HR software that helps you stay compliant
Personio’s specialised platform protects HR and employee data–keeping you compliant with relevant privacy regulations.
Maximise data security with Personio’s digital employee fileFAQs: HR Data Security & GDPR UK
What is HR data security under UK GDPR?
HR data security is the obligation to protect employee personal data against unauthorised access, loss, or misuse, as required by the UK GDPR and the Data Protection Act 2018. Under Article 32, employers must implement technical and organisational measures appropriate to the risk their processing presents.
What employee data is protected by GDPR?
All personal data relating to employees is protected – from names, addresses, and job titles to bank details, health records, right-to-work documents, performance appraisals, and disciplinary records. Health data, trade union membership, and biometric data are classified as special category data under Article 9 and require additional safeguards and a specific processing condition.
How do I respond to a DSAR?
Acknowledge receipt, verify the requester's identity using proportionate measures, search all systems where personal data may be held, compile the response (including supplementary information about processing purposes, retention periods, and rights), and deliver it free of charge within one calendar month of receiving the request.
What are the penalties for HR data breaches in the UK?
The ICO can issue fines of up to £17.5 million or 4% of global annual turnover (whichever is higher) for the most serious breaches. Less serious procedural failures carry a lower maximum of £8.7 million or 2% of turnover. In practice, fines are determined case by case based on the severity of the breach, the number of people affected, the organisation's culpability, and how promptly and cooperatively it responded.
Do I need to report all data breaches to the ICO?
No. Only breaches that are likely to result in a risk to the rights and freedoms of individuals need to be reported to the ICO, and this must be done within 72 hours of becoming aware of the breach. If the risk is low, you do not need to notify the ICO, but you must document the incident and your risk assessment. All breaches, notifiable or not, must be recorded internally under Article 33(5).
How long should I keep employee records in the UK?
Retention periods vary by record type. Payroll records should be kept for 6 years from the end of the relevant tax year, in line with HMRC requirements. Right-to-work documents should be retained for 2 years after employment ends. Recruitment records for unsuccessful candidates are typically kept for 6–12 months. Disciplinary and grievance records are usually kept for 6 years post-employment to support defence against potential tribunal or civil claims. Sickness absence records are generally kept for 3 years, extending to 40 years or more where exposure to hazardous substances is involved.
Can I transfer employee data to the US?
Not without additional safeguards. There is currently no adequacy decision between the UK and the US. If you use a US-based HR software platform, payroll provider, or send employee data to a US parent company, you need an International Data Transfer Agreement (IDTA) or Standard Contractual Clauses (SCCs) with a UK addendum, plus a Transfer Impact Assessment to document that the data is adequately protected.
Is employee monitoring allowed under GDPR?
Yes, within clear limits. You must have a lawful basis for monitoring, be transparent with employees about what is monitored and why, and ensure monitoring is proportionate to the purpose. Covert monitoring is only justifiable in exceptional circumstances, such as a suspected criminal investigation, and must be authorised by senior management.
What security measures does GDPR require for HR?
Article 32 requires 'appropriate technical and organisational measures', what is appropriate depends on the nature of the data and the risks involved. For HR data, appropriate measures typically include: encryption of data at rest and in transit, role-based access controls, multi-factor authentication, audit trails, regular staff training, automated backups with tested recovery, and a documented breach response procedure.
What is a Data Protection Impact Assessment (DPIA)?
A DPIA is a structured assessment of the data protection risks associated with a new processing activity. Under Article 35 of the UK GDPR, a DPIA is mandatory for processing that is likely to result in a high risk to individuals, including systematic monitoring of employees, processing biometric data, or introducing AI-based recruitment tools.
Do I need a Data Protection Officer (DPO) for HR?
In the private sector, a DPO is only mandatory under UK GDPR if your organisation is required to carry out large-scale, systematic monitoring of employees, or if you process special category data on a large scale as a core activity. Most mid-market employers are not legally required to appoint a DPO, but many do so as a matter of good practice, particularly where HR processes involve significant volumes of sensitive employee data.
What are the most common HR data breaches?
The most frequently occurring HR data breaches involve: accidental disclosure – payroll or employee files emailed to the wrong recipient; lost or stolen devices containing unencrypted employee data; phishing attacks that compromise HR system credentials; misconfigured cloud storage making employee records publicly accessible; and failure to revoke access for former employees.
How do I prepare for an ICO audit?
Start by ensuring your Article 30 processing register is up to date and covers all employee data processing activities. Review your employee privacy notices. Complete DPIAs for any high-risk HR processing. Ensure you have signed Data Processing Agreements with all third-party vendors who handle employee data. Document your DSAR process and maintain records of past responses. Test your breach notification procedure. Run annual GDPR training for all staff handling personal data, and keep attendance records.
What security certifications should HR software have?
Look for ISO 27001 (information security management), SOC 2 Type II (third-party audited security controls over time), and for UK-focused vendors, Cyber Essentials or Cyber Essentials Plus. ISO 27701 (privacy information management) is increasingly relevant given the overlap between information security and GDPR compliance.
Can employees request deletion of their HR records?
The right to erasure under Article 17 is not absolute. In an HR context, employees can request deletion of their data, but you can refuse if you have a legitimate reason to retain it, for example, if you need the data to defend a potential legal claim, comply with an HMRC requirement, or fulfil a legal obligation.
What is the difference between a data controller and a data processor in HR?
As an employer, you are the data controller, you determine the purposes for which employee data is processed and the means by which it is processed. Your HR software vendor, payroll provider, or background check service is typically a data processor, they process employee data on your behalf and under your instructions.
Sources:
ICO – A guide to data security
ICO – Security outcomes
ICO – Time limits for responding to data protection rights requests
ICO – Penalties
ICO – Capita fined £14m for data breach affecting over 6 million people (press release, 15 October 2025)
ICO – Enforcement actions register https://ico.org.uk/action-weve-taken/enforcement/
ICO – Data (Use and Access) Act 2025: data protection and privacy changes
GDPR Register – ICO fines British Airways £20m for data breach (republication of ICO press release, 16 October 2020 — original ICO page no longer available online)
GOV.UK – Data (Use and Access) Act 2025: data protection and privacy changes
Personio – Security and Trust Center
Sources last checked on 10-04-2026.